Ledger Live Login — Complete Security Guide for Safe Crypto Management
Explore how to safely log into Ledger Live, understand how hardware wallets work, prevent phishing, and manage multiple blockchain assets with confidence and clarity.
Why Ledger Live Login Is Critical for Crypto Security
Ledger Live is more than a simple dashboard — it is the interface through which users interact with their cryptographic assets.
But the real security foundation lies in the **hardware wallet itself**, where private keys remain isolated from the internet using cold storage.
Logging in incorrectly or using a fake interface exposes users to scams, malware, and phishing operations that can drain funds instantly.
This guide walks you through safe login procedures while strengthening your understanding of private keys, transaction signing, and decentralized security concepts like blockchain verification and Web3 connectivity.
But the real security foundation lies in the **hardware wallet itself**, where private keys remain isolated from the internet using cold storage.
Logging in incorrectly or using a fake interface exposes users to scams, malware, and phishing operations that can drain funds instantly.
This guide walks you through safe login procedures while strengthening your understanding of private keys, transaction signing, and decentralized security concepts like blockchain verification and Web3 connectivity.
What Ledger Live Does
Ledger Live helps you:
Signing always happens on the physical device — a crucial distinction that protects users even if their computer is compromised.
- Monitor balances across multiple coins
- Send and receive transactions
- Install firmware updates
- Access DeFi, NFTs, and Web3 apps
- Manage accounts on chains such as BTC, ETH, SOL, and more
Signing always happens on the physical device — a crucial distinction that protects users even if their computer is compromised.
A Cautionary Tale: The Fake Login Trap
Oliver searched for “Ledger Live login” after buying a Nano X.
A polished clone website appeared, complete with graphics and instructions.
The page asked him to “connect the device and confirm recovery words.”
Fortunately, Oliver realized something felt wrong — because **Ledger never asks for recovery phrases online.**
Had he proceeded, attackers would have accessed the keys instantly.
**Using only the official Ledger Live application eliminates these risks.**
A polished clone website appeared, complete with graphics and instructions.
The page asked him to “connect the device and confirm recovery words.”
Fortunately, Oliver realized something felt wrong — because **Ledger never asks for recovery phrases online.**
Had he proceeded, attackers would have accessed the keys instantly.
**Using only the official Ledger Live application eliminates these risks.**
Safe Ledger Live Login Workflow
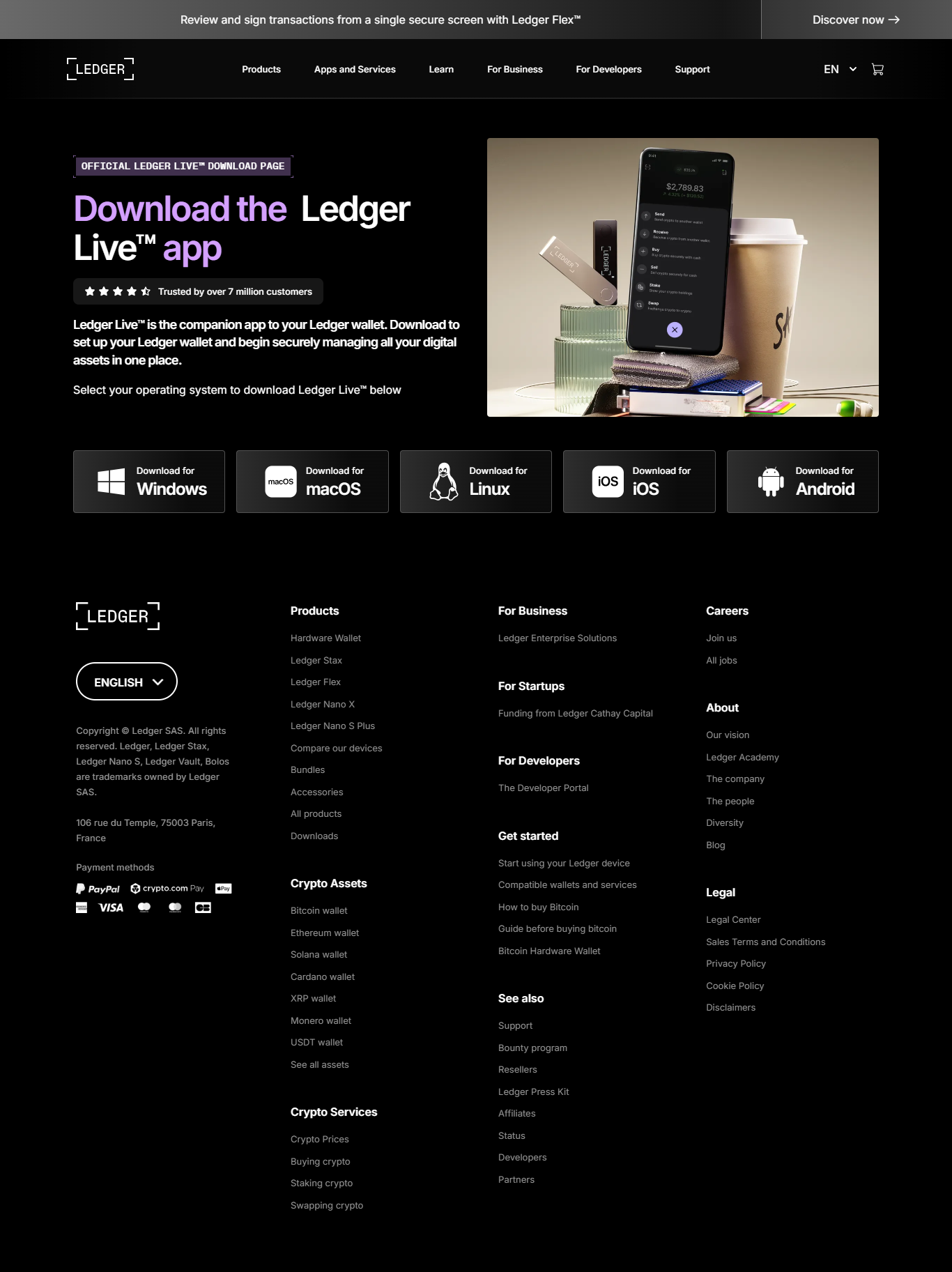
1. Download From the Official Source
Always use Ledger.com — never search results or ads.
2. Open Ledger Live
Launch the app after installation.
3. Connect Your Ledger Device
USB or Bluetooth depending on your model.
4. Enter Your PIN on the Device
Never type it into the computer — the hardware always handles authentication.
Understanding Ledger’s Security Architecture
Ledger uses a combination of:
Even if your computer is compromised, attackers cannot access the keys, because the signing process occurs entirely offline.
- Secure Element chips
- Isolated signing environments
- Physical verification screens
- Cold storage principles
Even if your computer is compromised, attackers cannot access the keys, because the signing process occurs entirely offline.
Wallet Comparison
| Wallet Type | Security | Key Control | Ideal For |
|---|---|---|---|
| Ledger Hardware Wallet | Very High | User | Cold storage |
| Hot Wallet | Medium | User | Daily use |
| Exchange Wallet | Low | Exchange | Trading |
Security Best Practices
✔ Install Ledger Live only from the official domain
✔ Never share your seed phrase
✔ Keep your recovery phrase offline
✔ Confirm transactions directly on the device
✔ Avoid third-party apps claiming Ledger compatibility
✔ Enable passphrase protections when appropriate
✔ Never share your seed phrase
✔ Keep your recovery phrase offline
✔ Confirm transactions directly on the device
✔ Avoid third-party apps claiming Ledger compatibility
✔ Enable passphrase protections when appropriate
Frequently Asked Questions
1. Does Ledger Live store my private keys?
No — keys remain inside the device.
2. Does Ledger Live require a password?
No — authentication uses the device PIN.
3. Is Ledger Live safe?
Safe when downloaded from the official source.
4. Can I manage many coins?
Yes — thousands across multiple chains.
5. What if my device is lost?
Restore using your recovery phrase.
No — keys remain inside the device.
2. Does Ledger Live require a password?
No — authentication uses the device PIN.
3. Is Ledger Live safe?
Safe when downloaded from the official source.
4. Can I manage many coins?
Yes — thousands across multiple chains.
5. What if my device is lost?
Restore using your recovery phrase.
Conclusion — Secure Login Protects Your Assets
Ledger Live provides an intuitive interface, but the true strength lies in the hardware wallet’s offline architecture.
Safe login practices, authenticity verification, and physical transaction confirmations build a multilayer defense that keeps your crypto secure even in hostile environments.
By following the official workflow, avoiding phishing links, and trusting the device rather than web pages, you ensure that your assets remain under your control.
Your security begins the moment you log in — choose the official path every time.
Safe login practices, authenticity verification, and physical transaction confirmations build a multilayer defense that keeps your crypto secure even in hostile environments.
By following the official workflow, avoiding phishing links, and trusting the device rather than web pages, you ensure that your assets remain under your control.
Your security begins the moment you log in — choose the official path every time.